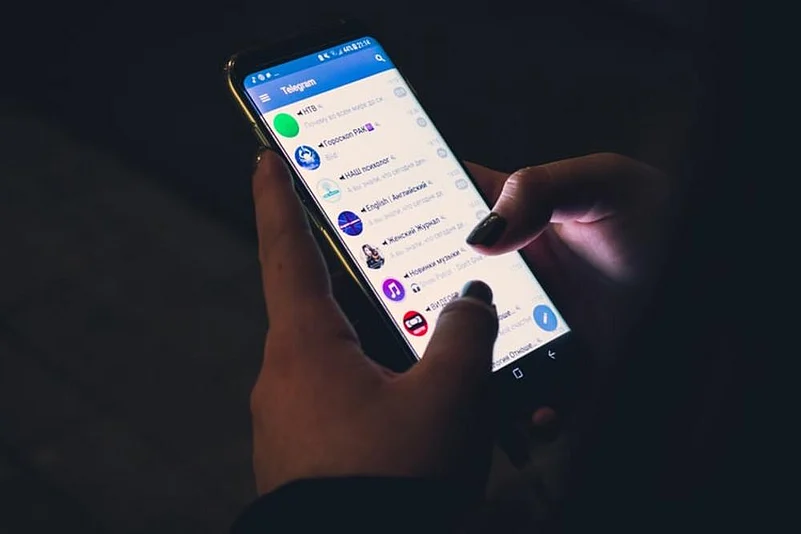
Amidst instant messaging mobile application WhatsApp, receiving a lot of flak for its recent privacy policy, with users fearing for their data, terrorist groups in Pakistan have shifted base to new messaging applications, officials in Srinagar said.
Three new mobile applications are being scrutinised after evidence was collected following encounters with terrorists and based on information gathered from those who surrendered before the Indian Army, officials said adding that the names of these messaging apps have been withheld for security reasons.
While one of the applications is owned by a company based in the United States, the second is based in Europe. The third is an application developed by a Turkish company that has been frequently used by terrorist handlers and their prospective recruits in the Kashmir Valley, officials said.
Advertisement
The new applications have the ability to work with the slowest internet connection where Enhanced Data for Global Evolution (EDGE), used in the late 2000s, or 2G is in operation.
The government had suspended internet across Jammu and Kashmir after the abrogation of the special status of the erstwhile state in August 2019. Early last year, 2G internet services were restored.
Terror groups had virtually stopped using WhatsApp and Facebook Messenger. Later, it was found that they have switched over to new applications available free of cost on the world wide web, a security official said.
All encryption and decryption happen directly on the devices, therefore, reducing third party intervention at any point and these apps use encryption algorithm RSA-2048 which was adopted as the most secure encrypted platform.
Advertisement
RSA is an American Network Security and Authentication company that was founded in 1982 by US-born Ron Rivest, Israeli-born Adi Shamir and US-born Leonard Adleman. The acronym RSA is used worldwide as the foundation key in the cryptosystem.
One of the new messaging apps used by terrorists to radicalise the youth in the Valley does not even ask for phone numbers or emails for enabling complete user anonymity, the officials said.
Efforts are on to block such applications in Jammu and Kashmir, they said.
This comes at a time when the security agencies in the Valley are fighting the menace of virtual SIM cards. Terror groups have been increasingly using these to connect with their handlers in Pakistan.
The penetration of this technology came to light in 2019 when a request was sent to the United States to seek details from a service provider of virtual SIMs used by a Jaish-e-Mohammed suicide bomber in the attack on a CRPF convoy in Pulwama that left 40 personnel dead.
However, a detailed investigation done by the National Investigation Agency and other security agencies indicated that over 40 virtual SIM cards were used in the Pulwama attack alone, and there are probably more of them floating in the Valley's cyberspace, the officials said.
It is a fairly new modus operandi wherein terrorists from across the border are using virtual SIM cards generated by a service provider based in a foreign country. In this technology, the computer generates a telephone number and the user needs to download an application of the service provider on his or her smartphone to use it.
Advertisement
(With PTI inputs)